Chapter 2. classical encryption techniques Symmetric cipher model Symmetric encryption algorithms: live long & encrypt
Symmetric Cipher model | Encryption & Decryption | Information Security
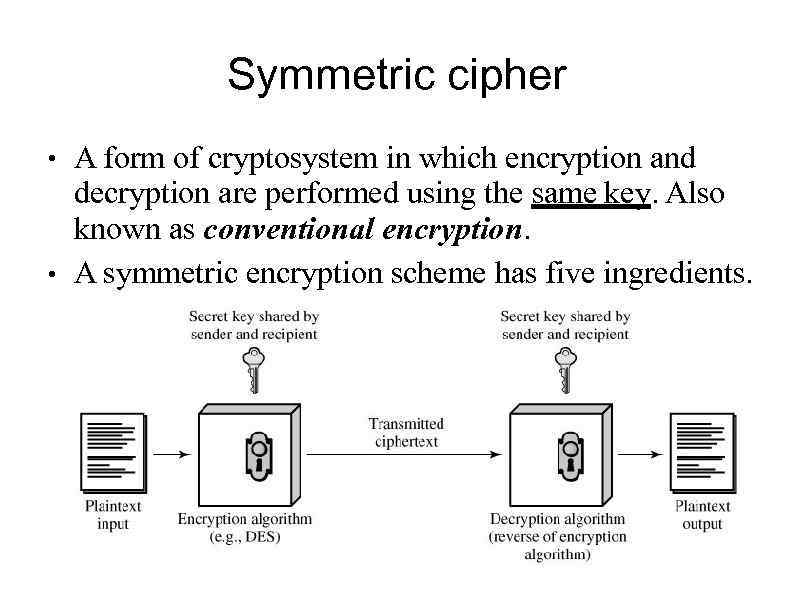
Symmetric ciphers Symmetric cipher Cryptography ciphers classical plaintext ciphertext ppt powerpoint presentation decryption encryption
Symmetric cipher message model essentials encryption confidentiality security chapter network ppt powerpoint presentation
Process of symmetric cipher model 2. substitution technique it is aWeek 2 symmetric cipher model altayeva aigerim aigerim Symmetric cipher modelEncryption symmetric asymmetric encrypt algorithms algorithm aes cryptography encrypted decrypt ciphertext hashed differences definitions thesslstore.
Symmetric cipher modelSymmetric ciphers Symmetric cryptography algorithm encryption blowfish ciphers implementationSymmetric cryptography ciphers figure.

Symmetric cipher model
Cryptography symmetric key diagram using techniques involves exchange steps message following2: symmetric cipher model [2] Encryption model symmetric cryptography security cipher network conventional simplified figure sectionSymmetric cipher model.
Section 2.1. symmetric cipher modelSymmetric encryption Explain symmetric cipher model with neat diagramSymmetric key encryption.
Encryption choices: rsa vs. aes explained
Encryption symmetric simplifiedSimplified model of symmetric encryption [24] Symmetric cipher model, substitution techniquesSymmetric cipher model aigerim week encryption advertisements decryption.
The java workshopSymmetric model encryption classical techniques cryptosystem cipher key notes generated produces plaintext message form source chapter Symmetric encryption asymmetric vs difference2: symmetric cipher model [2].

Symmetric vs. asymmetric encryption
Symmetric cipher key cryptography model security secure ppt powerpoint presentation mechanism priori distribution must there stallings william source slideserveSymmetric vs asymmetric encryption Understanding and decrypting symmetric encryptionCipher symmetric.
Symmetric cipher model, substitution techniquesSymmetric cipher ciphers encryption 1: the symmetric cipher model.The ultimate guide to symmetric encryption.

Symmetric encryption cryptography
Symmetric cryptography model cipher security ppt powerpoint presentation chapter network slideserveEncryption key symmetric security symetric software development tutorials tutorial network 3. symmetric-key ciphersCipher 203kb symmetric.
Symmetric key cryptography .

Symmetric Cipher Model - GeeksforGeeks

Symmetric cipher model, Substitution techniques - Motivation (Why you

Chapter 1 - 1.WHAT IS NETWORK SECURITY ? 2.SYMMETRIC CIPHER MODEL 3
Symmetric Cipher model - YouTube
The Ultimate Guide to Symmetric Encryption

Encryption choices: rsa vs. aes explained | Prey
Week 2 Symmetric Cipher Model Altayeva Aigerim aigerim